I couldn’t find a suitable title for this post, in which I try to gather various insights that I’ve received in the past few days and that I’ve planned, sooner or later, to discuss together with Rocco Sicilia.
I’m discussing the IEC 62443 certification with an organization: that build and sell ICS plants which are risky from a safety perspective. They currently comply with the Machinery Directive (Directive 2006/42/EC of the European Parliament), but they are not considering the Cyber risk.
Managing Cybersecurity is expensive, we all know that. But not managing it is also more expensive. Given my experience, an SME recovers from a critical Cyberattack in 5-10 days, if it can recover (yes I also personally know companies that lost everything because of a Cyberattack).
Many companies (hopefully) are collecting logs in a central system. The reason besides that is for compliance and sometimes for root cause analysis. In this post, I want to recap that log management is not just about log collections, and why and how the process should be designed.
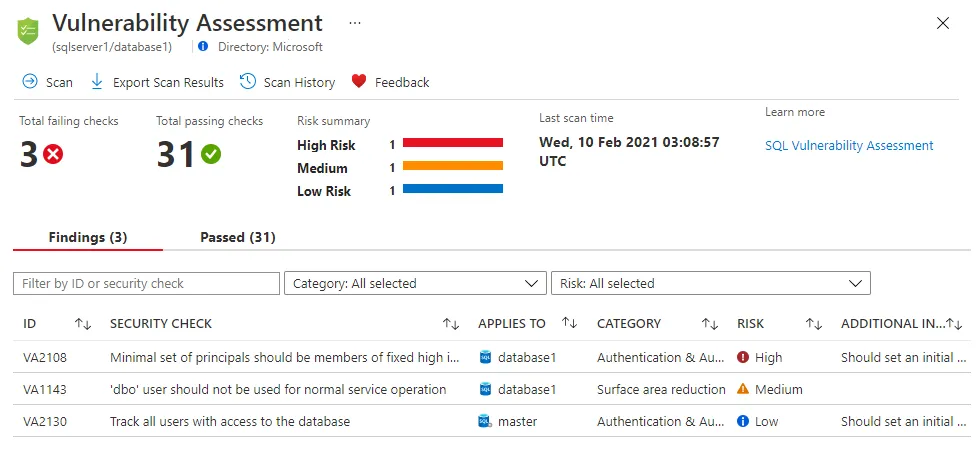
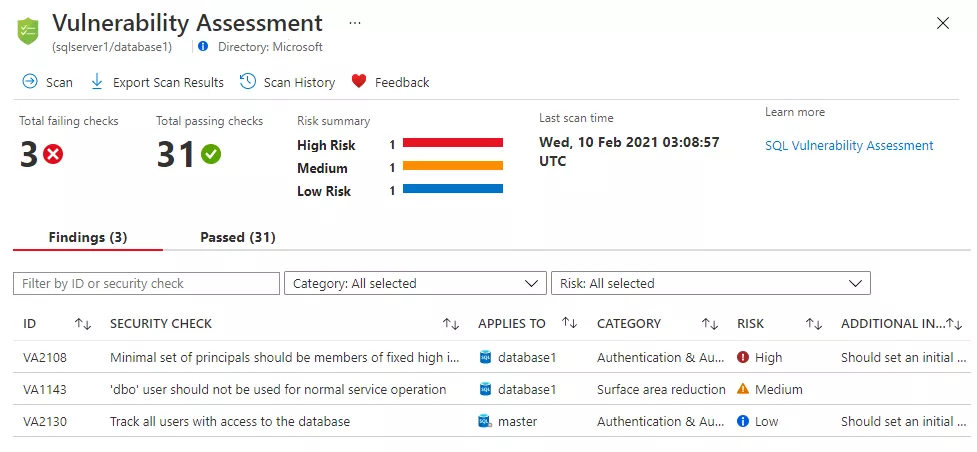
In this article, I’m explaining why we are executing VA, why the traditional approach is dangerous and how we should manage the risk bound to vulnerabilities. I’m also discussing a few false myths about VA.
Nowadays (hopefully) all companies are executing regular vulnerability assessments. They often use different partners/tools each year and they often limit themselves to vulnerability assessments. VAs are not the end of a security strategy, they are just a small step at the beginning.
A few days ago, together with Rocco Sicilia and FESTO Academy , I presented a webinar on OT/ICS Cybersecurity approach. We are often spending time increasing Cybersecurity awareness, and that webinar was focused to gives Cybersecurity fundamentals to OT managers.
We’re leaving in the ‘hype’ era, where everything is sold as the Holy Grail for a non-real problem. Let’s try to analyze things with a critical eye. Pushed by a friend, who is writing a couple of very good posts I recommend, I’m now sharing my thoughts about automation, the future of network engineers, AI, and so on.