Nautobot automation series
July 12, 2024
Cybersecurity: fashion or strategy
I couldn’t find a suitable title for this post, in which I try to gather various insights that I’ve received in the past few days and that I’ve planned, sooner or later, to discuss together with Rocco Sicilia.
I start with the provocation: the world of Cybersecurity has certainly been under the spotlight for some years now. Provocatively (we’ll see the reasons later), I would define it as “trendy”. There are various hypes that follow one another in creating needs/fears with the aim of selling solutions and services. There’s nothing wrong with this, but we need to distinguish acting out of “trendiness” from strategic action.
Acting out of “trendiness” is an impulse, aesthetic, sometimes very personal, often done out of emulation, and fundamentally it’s difficult to trace the motivation behind some choices. Because it’s precisely an impulse. Translated, for the purpose of this post, security measures chosen on impulse are not guided by a strategy and, we have already talked about this several times, they are often ineffective. This mode is extremely widespread and easy to identify: if I ask “why” a security measure (NAC, firewall, Security Awareness Training Software…) was implemented, the answer tends to be (I exaggerate and simplify) “because”. Almost always, these security measures chosen on impulse are not integrated into a process and are not monitored (we have also talked about this).
Strategic action (summarized) starts with an analysis and inserts security measures into a higher design. Each measure is chosen and inserted with a specific purpose and measured as such. There may be exceptions but they are well documented and temporary (with a certain date). Because an exception weakens the protections we have implemented.
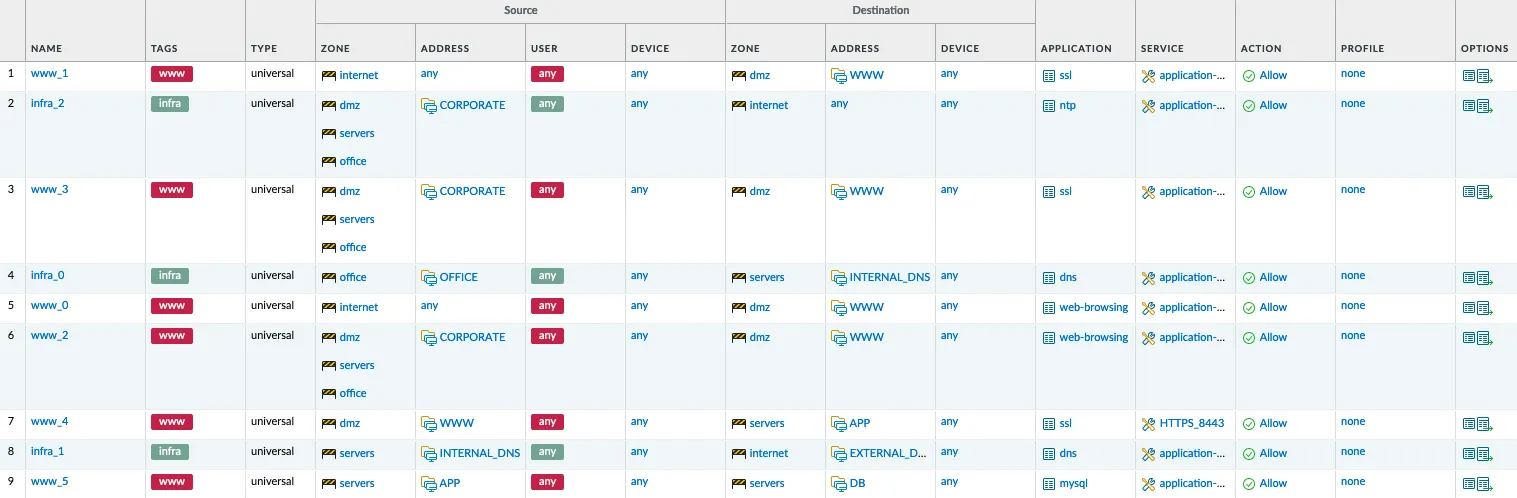
A real example that touches on the fundamentals: the firewall. All companies have a firewall, whether it’s perimeter, dual bastion… But almost no company defines policies: policies are made by technicians and are often hated because they limit others’ work. Strategic action starts from the purpose of one’s infrastructure, which is to support the business. As such, it must provide services that are implemented through servers. These servers, to function, have connectivity needs and therefore risks. Risks are mitigated by dividing servers into areas and these areas can only communicate with each other under certain rules, which are translated into firewall policies. In the ideal world, I should NEVER find systems publicly exposed and positioned in networks considered secure. However, I find them and they are often historical relics, abandoned, unchecked but, precisely exposed for “historical reasons”.
Because, in companies, security is done by technicians, there is no strength to bring the world of Cybersecurity to the corporate level.
And then the CISO arrives.
The responsibility for Cybersecurity is dumped onto the CISO. And I mean “dumped”: namely, the problem, once relegated to technicians, is now relegated to a manager so that the company can continue to forget about it. Let’s start with the basics:
- a CISO who doesn’t report to the board cannot do his job;
- a CISO who doesn’t have a budget cannot do his job;
- a CISO who doesn’t have veto power cannot do his job;
- a CISO who is not consulted before any technological choice cannot do his job.
It has been said many times: Cybersecurity is a corporate problem, but everyone keeps pretending otherwise. A couple of years ago, I had the opportunity to interview some CEOs of enterprises close to me. The answers were enlightening because they allowed me to enter their mindset and understand their needs. In short: Cybersecurity is not a topic of interest to them, because it’s delegated to the CIO / CISO (depending on the company).
Of course, there are many exceptions, but the dominant behavior I notice is the one I described.